01
Compliance Advisory
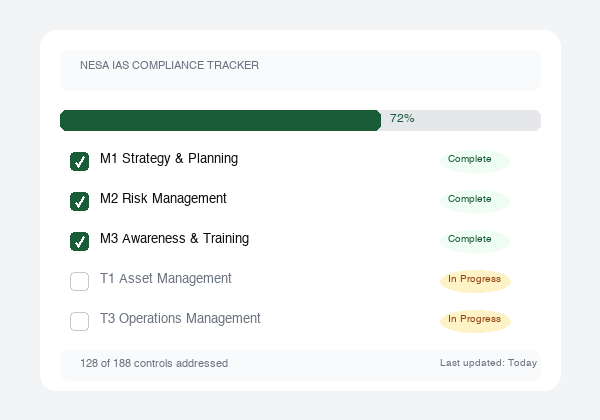
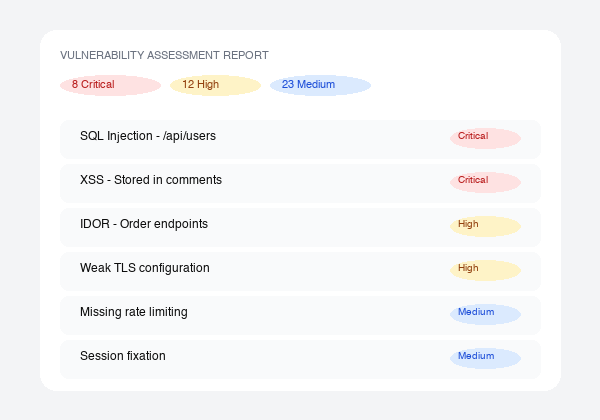
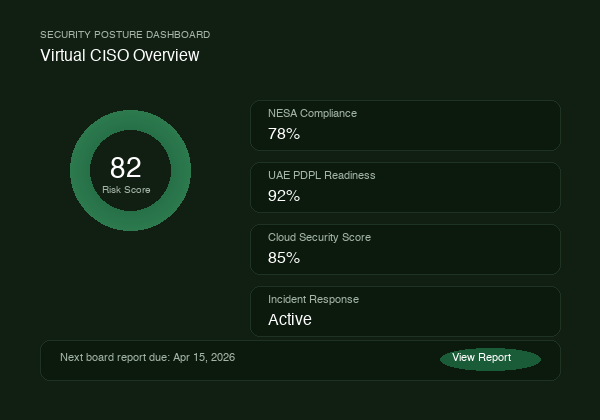
The UAE's regulatory landscape has more frameworks, enforcement mechanisms, and overlapping requirements than most organizations realize. We take you from initial gap analysis to audit-ready status across NESA, ISO 27001, PCI DSS, SOC 2, and UAE PDPL, with documented evidence, board-ready reporting, and a clear remediation roadmap at every stage.
- NESA/SIA IAS: all 188 controls mapped and addressed
- ISO 27001 implementation and certification support
- PCI DSS v4.0 readiness assessments
- SOC 2 Type I & II preparation
- UAE PDPL compliance and readiness programs
- DPO readiness and appointment support
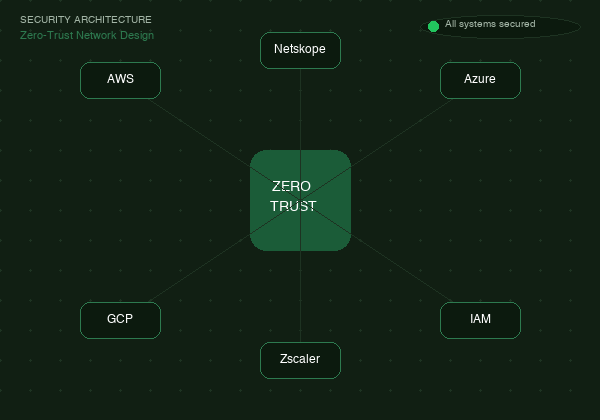
- DESC cloud security standards for Dubai-based entities
✦ Typical engagement: 6 to 16 weeks
Start a Compliance Assessment